With the recent roll out of end to end encryption by Whatsapp, the largest messaging service, everyone has been talking about it. The FBI vs Apple battle over privacy debate is a minor one if one sees the implementation of end to end encryption in an online messaging application. There are a ton of companies that brag about their services are encrypted. What this means is that the messages being sent using the communication platform are secure and hackers cannot read them if they somehow manage to get in the middle of the two people communicating. That is, even if someone gets access to the channel being used by the people communicating, for example your network administrator (or any other person who has access to your network, commonly known as man in the middle attack), they cannot read the contents of the message being sent.
Encryption, what?
It is the process of encoding information in such a way ensuring that only authorized people can understand (or read) it. The process involves a key, which is used to encrypt the data. The key is responsible for encrypting the data into an encoded message, and depending on the type of encryption, only a specific key can be used to decrypt the message to its original form.
What is the advantage of end to end encryption?
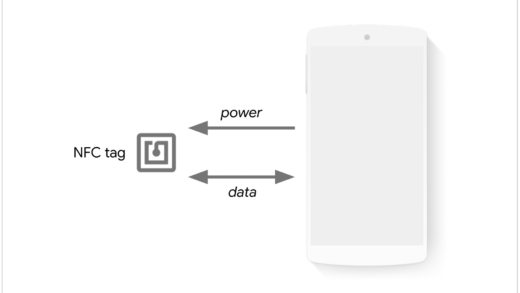
End to end encryption is a form wherein only people who are communicating have the keys to decrypt the messages. No eavesdropper can have access to these keys, and not even the company that is running the platform. Therefore, no hacker, or any government organization can stand over the organization’s shoulder and make them decrypt the messages. Technically, it is not impossible, but end to end decryption is one of the safest ways to ensure privacy. This also gives a blow to government authorities like FBI who try and pressure the messaging platforms to decrypt the message. The company’s servers do not have any information about the messages being sent and they only act as puppets passing a message without really knowing what it means. The keys never leave the user’s device and hence the server can never know anything about it. Many people might be confused that the keys must be interchanged at least once, but that does not happen at all, thanks to public key encryption. A pair of private and public keys are generated. The public key can be shared with everyone. Messages encrypted using the public key, can only be decrypted using the private key (the combination of keys is made such, thanks to mathematics). Hence no one can understand what messages were send until they have the key. Hence end to end encryption makes your privacy a top concern.
![whatsapp-security[1]](https://wisdomgeek.com/wp-content/uploads/2016/04/whatsapp-security1.jpg)
For those who are still confused about public key encryption, here’s a video explaining it:
Of course there are workarounds to everything in technology. Example, Apple uses end to end encryption in iMessages, but it also backs it up to iCloud, which makes use of a different key. Hence they can access your messages if they are pressurized to. Other ways of breaking in can be a man in the middle attack, or attacking the ends. After all a mail is only as secure as are the mailboxes receiving the emails.
But overall, WhatsApp has taken a huge step by partnering with Open Whisper Systems to implement end to end encryption across all the platforms it supports. And the move makes the process of decrypting WhatsApp messages require extraordinary measures.